DAM Insights Your Entire Organization Will Actually Use
Your DAM can feel like an overwhelming tool to report on. Everyone wants something different from it. Learn more.
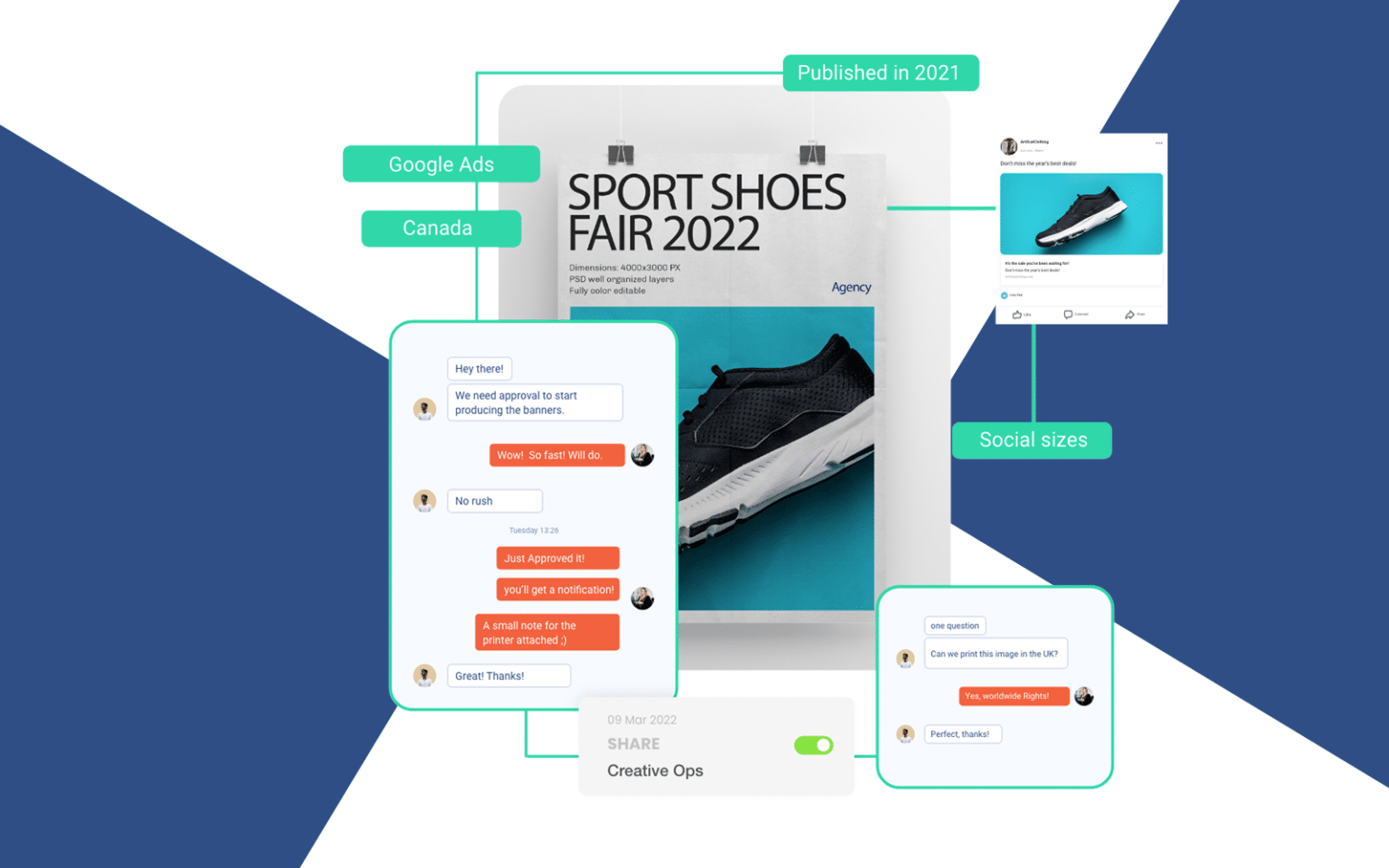
Transform your DAM from an archive into a publishing powerhouse
Let’s face it—traditional DAM software isn’t built with the needs of today’s modern marketing teams in mind.
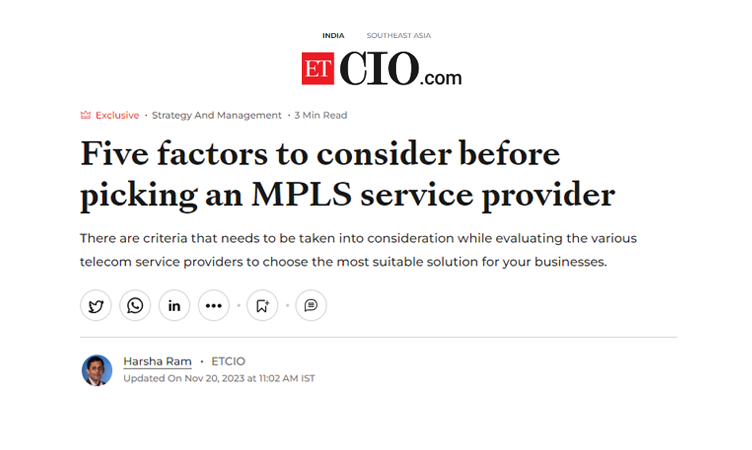
Five factors to consider before picking an MPLS service provider
In today’s hyper-connected and fast-paced global marketplace, connectivity is the lifeblood needed to keep businesses running smoothly. Enterprise, small or large, need reliable and fast communication networks to work and grow.
Organizations are given access to a communication network that is entirely dependable, quick, flexible, and cost effective due to MPLS and its “labelling protocol” Businesses are considering shifting to MPLS networks due to the clear advantages of MPLS connectivity, However, choosing an MPLS service provider can be time-consuming and complicated given the industry’s diverse offerings and management methods.
There are criteria that needs to be taken into consideration while evaluating the various telecom service providers to choose the most suitable solution for your businesses.
The first element that businesses need to check is the network coverage offered by the service provider. It is critical to confirm that the network carrier’s service area includes all your targeted locations, and if global connectivity is required, the network service can provide reliable international coverage. Therefore, latency, jitter, resilience, and cost of the MPLS network are all directly impacted by the service providers’ reach and coverage.
The second criteria is to consider the Network Project Management and Monitoring, because complex networks require constant management to run smoothly. Proactive management can result in reduced expense, fewer outages, and enhanced security. Therefore, the specifics of pricing and the range of services offered under the heading of network management and monitoring services must be understood by businesses.
In order to free up IT employees, it is also crucial to check whether the service provider monitors the entire network and provides managed services.
The third criteria to be mindful about while choosing an MPLS service provider is their Network Security. Security capabilities of the MPLS service provider need to be scrutinized closely. Businesses need to ensure that service providers can support and monitor the entire network closely and provide access to a dedicated security infrastructure, including experienced NOC engineers to ensure guaranteed uptime.
Another sure-fire way to assess the capabilities of the service provider is to check the SLAs (Service Level Agreements) offered. While experienced service providers with tested capabilities are usually willing to back their services with SLAs, it pays off to compare SLAs of several MPLS network providers. It is also helpful to look at their existing clients and check references to evaluate their performance.
Subsequent to comparing SLA’s, it is important for businesses to assess, evaluate and understand the Class of Service (CoSs) and Quality of Service (QoS) offered by the carrier. The Quality of Service (QoS) is impacted by the carrier’s consolidation and prioritisation decisions for different traffic categories. These standards must comply with the requirements of your business, and the contract with the service provider must specifically describe and list these service commitments.
While the mentioned points form a base to shortlist the right MPLS network provider, other factors such as routing protocols, staff expertise, 3rd party partnerships, network architecture and future scalability capabilities must also essentially be a part of the decision making process.
Despite the fact that cost is a major consideration in any business decision, your company’s long-term objectives and alignment with current and future needs should ultimately take precedence. After all, your MPLS Network will form the backbone of your business while looking at it from a wider perspective.
How to improve your team’s velocity by tracking and measuring lead time?
Credits: Published by our strategic partner Kaiburr
Digital transformation has turned every organization into a software company, regardless of the industry they are part of. Companies are required to react faster to changing customer needs but on the other hand, deliver stable services to their customers. In order to meet these requirements, DevOps teams and lean practitioners have to constantly improve themselves.
DORA metrics addresses this need by providing objective data to measure the performance of software delivery teams and drive product improvement.
What are DORA metrics?
To determine the right metrics to track the effectiveness and efficiency of software teams, DevOps Research and Assessment team came up with four metrics that can be used by teams to measure their performance and find out whether they are “low performers” to “elite performers”.
The four metrics used are deployment frequency (DF), Lead time (LT), Mean time to recovery (MTTR), and Change Failure Rate (CFR).
Out of these four metrics Lead Time measures the amount of time needed to implement, test, and deliver changes to the codebase. This metric measures the time between work packet creation till its completion into production. It is one of the measures of software delivery performance also known as Development Velocity.
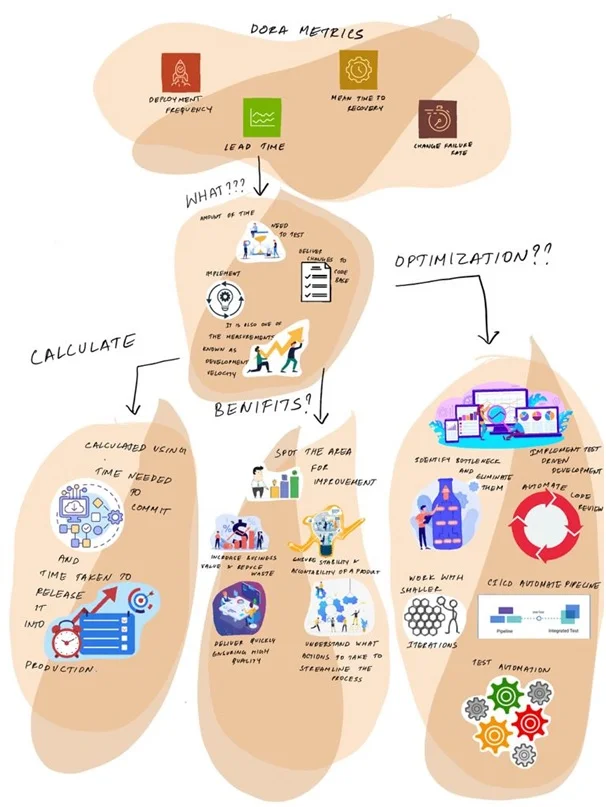
Benefits of implementing Lead Time
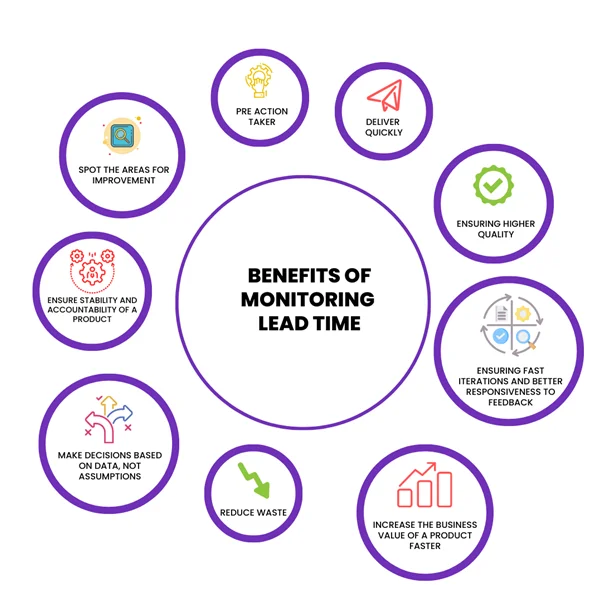
Lead Time metrics help a team to:
- Spot the areas for improvement when it comes to the delivery process
- Understand what actions to take to streamline the process
- Deliver quickly, ensuring higher quality
- Ensure stability and accountability of a product
- Make decisions based on data, not assumptions
- Spot problems like the lack of people or inefficiency of testing
- Deliver more value to clients by ensuring fast iterations and better responsiveness to feedback
- Increase the business value of a product faster and reduce waste
Let’s try to understand Lead Time in more detail.
Lead Time: As mentioned earlier, it is the time from when request for a requirement/ feature gets raised to the time it gets released into production i.e., the total time elapsed from the creation of work items to their completion. It measures the time spent in development, testing, implementation and integration but does not include the time spent in backlog prioritization and design. Shorter product lead times enable faster feedback on what is getting built and allows for quick correction.
The lower the lead time for changes, the more efficient a DevOps team is in deploying code.
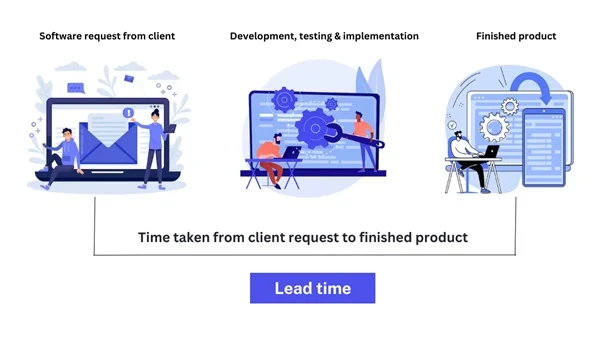
In order to measure Lead Time, two pieces of data (or timestamps) are required: The exact time of the commit and the exact time of the deployment – in other words, the time from start to finish of a product. The average time is then used as an indicator for overall performance.
The question this metrics answers is, how long does it take to go from code committed to code successfully running in production.
How to calculate Lead Time?
To measure Lead Time for Changes, we need two pieces of data:
- The time taken for commit
- The time taken to release it into production
To measure lead time, calculate the time elapsed between making a commit and releasing it to production.
Calculating lead time beginning after creating a task helps teams understand the full feature life cycle, including the design and planning stages.
Based on this metric, performance of a DevOps team can be divided into four categories as per the following benchmark:

- Elite Performers: Less than one hour
- High Performer: Between one day and one week
- Medium Performers: Between one month and six months
- Low Performers: More than months
Collecting Data
One of the ways to collect data is to simply ask developers for the average lead times. A better way would be with the help of a dedicated DevOps metrics platform.
Integrating the DevOps software and committing data into everyday tracking using an automated metrics platform will give you more accurate results that are easier to aggregate and analyze.
Why should we measure Lead Time?
Lead Time is an indicator of how quickly a team responds to needs and fixes. It represents the efficiency of the process, code complexity, and team’s capacity.
The metric helps to understand how long it takes to get changes to production. If Lead Time is too high, it shows inefficiencies and bottlenecks in the process hurting team velocity and morale. A short lead time shows that a team reacts to feedback and changes quickly, sets their industry’s pace for innovation, and ultimately wins the marketplace. The team’s goal should be to reduce Lead Time for changes and react to issues in a timely manner.
In high-performing organizations, developers integrate commits to the main branch with fewer roadblocks and less time is spent waiting. Hence, deploying features into production becomes effortless, automatic and smooth.
This metric is also essential while working with clients, who prefer to work with a team that responds to urgent bug fixes within hours.
Causes of high Lead Time
High Lead Time for changes is most often caused by inefficient processes and introducing too big changes to production. Other reasons are:
- Poor Definition of Ready
- Manual testing
- Blocks and dependencies
- Inefficient development process
- Complex routes to production
- Huge changes introduced to code
How to optimize Lead Time?
Optimizing and reducing lead time can be beneficial for a DevOps team and for the success of business.
To optimize Lead Time for Changes, a team has to:
- Work with smaller iterations – smaller changes will help developers to get feedback faster and resolve issues quickly.
- CI/ CD – Automate the pipeline – Continuous deployment is a commonly used strategy in software development process where each code commit or merged pull request is automatically released to production once it passes the automated testing stage. CI/CD integrates the continuous deployment strategy with continuous integration, a practice where code changes are made regularly.
By employing these two strategies, CI/CD enables development teams to deploy code to production more efficiently and quickly.
By implementing CI/CD, speeding up the delivery process and reducing manual tasks, lead time can be reduced substantially.
- Test Automation – Use automated tests at every stage of CI/CD pipeline to spot issues earlier and to make sure the build meets acceptance criteria.
Test automation replaces many of the manual checks for developers and also allows for any necessary changes to be made early in the development life cycle, reducing change failure rates. When you integrate CI/CD with test automation, you can reduce your overall lead time, allowing you to release products to customers at a much faster rate.
- Automate code reviews – Code review is one such process that involves a lot of manual intervention. Automating this activity helps to improve quality and save time.
- Implement Test Driven Development – Integrate testing into the development process i.e., Developers have to understand the requirement, create unit test cases, execute them and then move the code into the test environment. This initiative has the following benefits:
- Raises the level of code quality and guarantees that all procedures are carried out.
- Enables the developers to plan their code before writing the same thereby reducing the time required for development.
- Supports the development teams in delivering high-quality products with fewer bugs and cleaner code.
All these initiatives will have a significant effect in reducing the lead time.
- Identify bottlenecks and eliminate them – One of the initiatives is to identify the bottlenecks in areas like change approval, streamline the required processes and eliminate the processes which do not add any value.
By measuring and tracking Lead Time, a team can make better, more informed decisions about what can be improved and understand how to do that. When Lead Time improves, a team can be sure that they’re making good choices and delivering more value to customers and users of a product. A team should not only thrive to become an elite performer but also has to deliver better business value faster.
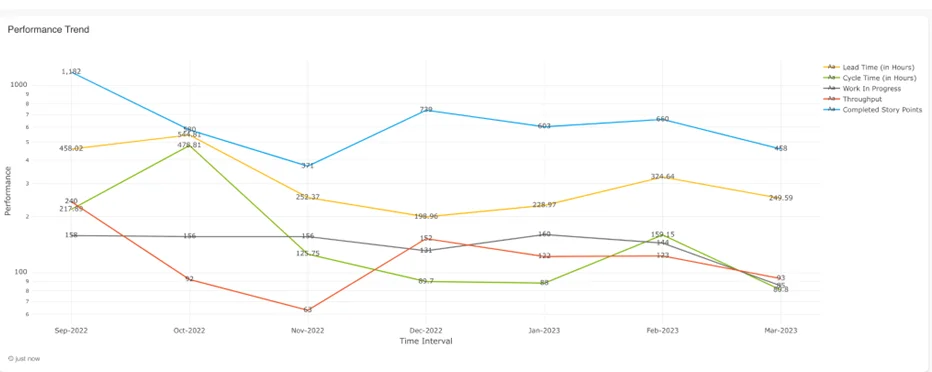
Kaiburr helps every product engineering team to measure their performance near real time using industry standard KPIs like those shown below –
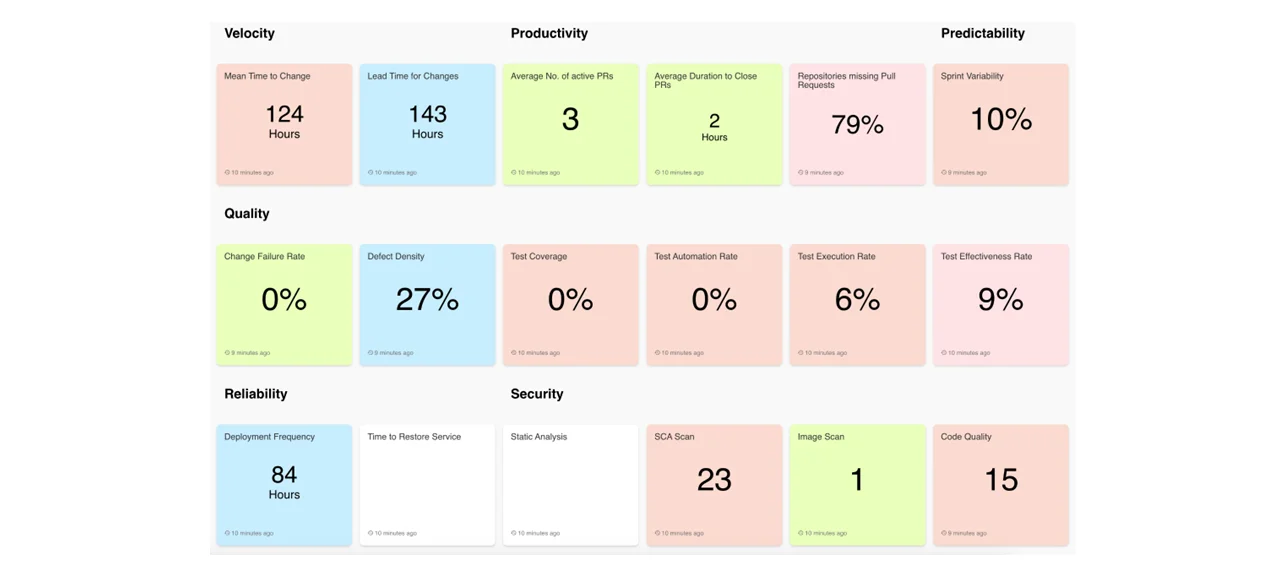
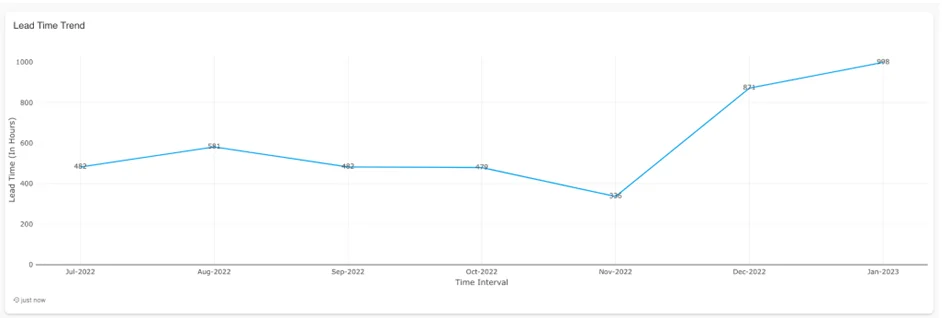
You can then drill down to specific trends in lead time for a portfolio, project, initiative, team, epic, sprint or release like the below –
You can also compare lead time with other KPIs to identify bottlenecks and improve –
If you want to get started with your Stage Gate Compliance journey using Kaiburr reach us at marketing@sifycorp.com
Credits: Published by our strategic partner Kaiburr
Reimagine your digital transformation with infusion of automation across multi-cloud and hybrid IT
The IT landscape is accelerating at an unprecedented rate powered by AI and cloud infrastructure. Businesses across industries are exploring the potential of hybrid IT in their digital transformation journey. Today, agility, resiliency and security are of paramount importance to businesses, as they continuously focus on innovation, scalability, operational efficiency, and growth.
By leveraging automation through AI/ML across hybrid cloud solutions, business leaders unlock a range of benefits, including embracing an automated agile, scalable, and secure platform while maintaining a cost-competitive edge amidst the changing market dynamics. Ultimately, all of this enables businesses to maximize the value of their investments, drive sustainable growth, faster go-to-market and shorter time to adapt.
However, before enterprises set out to build the right hybrid cloud ecosystem, business leaders need to address some critical key points following below:
- App stratification to adopt multi-cloud and hybrid IT
- Building the right architecture to adopt multi cloud and enabling hybrid IT
- Seamless migration milestone mapping to meet business objectives
- Visibility for right planning and productivity
- Unified platform driving cost savings, operational efficiency, and cloud governance
Understanding these key factors has a profound impact on maximizing the benefits that hybrid IT offers. Now, let’s look at the fundamentals of hybrid IT, its challenges, and how AI/ML helps in mitigating these challenges.
What constitutes Hybrid IT and makes it advantageous?
Hybrid IT refers to an IT infrastructure environment that combines elements of traditional on-premises or in-house data centers with cloud-based solutions. Hybrid cloud combines both public clouds as well as managed private clouds. It brings together the best of both worlds, allowing organizations to leverage the scalability and cost-efficiency of the public cloud for their elastic workloads and managed private cloud for fixed and regulated workloads.
Challenges while adopting multi-cloud and hybrid IT
While it has a lot to offer, hybrid IT infrastructure comes with its own set of challenges. Security & data protection, regulatory compliance, cloud sprawl, performance management, vendor lock-in, network complexity, and cost management are among the few challenges enterprises faces while adopting multi-cloud and enabling hybrid It. Let’s look at the two major challenges-
- Data Governance: As organizations navigate the complexities of managing data across both public and private cloud environments, ensuring data security and compliance becomes both difficult and paramount.
- Integration and Management: The technical challenges of integrating and managing diverse cloud platforms and technologies can be daunting. Ensuring seamless workload allocation, optimizing resource usage, and overcoming challenges in managing and analyzing large data sets for business intelligence is essential.
Mitigation plan for the challenges above
Analyzing your existing cloud infrastructure to transform it into a future-ready state that aligns with your organization’s strategic business objectives is the first step in your cloud journey. It will help you identify and address the real-time challenges while adopting multi/hybrid cloud. These challenges can be mitigated with the help of emerging technologies like Artificial Intelligence and Machine learning.
The infusion of AI and machine learning technologies takes hybrid cloud management to the next level. By creating a multiplier effect, the combination accelerates transformation with result-driven capabilities, such as intelligent automation, predictive and proactive analytics, and enhanced data processing. It enables enterprises to extract valuable insights from massive amounts of data and empower them to make data-driven decisions.
AI/ML can also optimize the management and utilization of hybrid cloud resources by dynamically allocating workloads, optimizing resource allocation, and ensuring efficient performance across environments, including predicting and automating recovery from failures. It also enables advanced security and compliance to identify and mitigate potential threats in real-time, detect anomalies and patterns, and proactively address security risks.
Enterprises can leverage AI/ML to make real-time decisions while running modern applications and derive insights across velocity of omnichannel data. An AI/ML enabled centrally managed platform on the cloud and edge locations can seamlessly sync data pipelines with multiple connectors from applications, APIs, and databases to data warehouses/lakes and back. This enables intelligent decision making with AI predictions from operations data at the edge. Also, it empowers customers with necessary architectural guidance and design.
Impact of AI/ML on FinOps
AI/ML-enriched hybrid cloud environments have a significant impact on FinOps by increasing overall productivity with substantial cost savings. AI/ML algorithms can be utilized to effectively manage and orchestrate several instances, virtual machines (VMs), containers, and legacy infrastructure components. Furthermore, natural language processing (NLP) and generative AI can be leveraged for hybrid cloud transformation, code debugging, and user experience (UX) improvement.
For instance, enterprises can identify customer segmentation by blending ML and existing techniques to deepen product expertise and marketing effectiveness. This directly drives down acquisition costs and increases retention rates.
It is important for enterprises to focus on resiliency and building security solutions
around data in rest and transit, while architecting the low-level design.
The resulting automation and decisive business intelligence helps to optimize resource allocation and cost management in the backend while enabling businesses to proactively address potential issues. AI/ML in hybrid cloud environments also influences customer focused business operations by unlocking enhanced customer experiences, improving response times, and driving higher customer satisfaction (CSAT) scores. By performing sentiment analysis, businesses can spot and prevent issues with the product experiences. This, in turn, positively impacts key performance indicators, turns reviews into actionable insights, and contributes to the organization’s success.
Sify’s Cloud Anywhere: Enhancing operational efficiency
With the changing business needs and market dynamics, enterprises must start investing in the right tools, technology, and partner that can assist them with change management, cost & risk management, and eliminating other challenges. Sify empowers organizations to navigate the complexities of multi cloud and hybrid IT environments with confidence. Our AI/ML-enabled hybrid cloud solutions provide a reliable foundation for successful digital transformation initiatives.
Sify’s Cloud Infinit is a next generation enterprise grade cloud infrastructure and managed services offering with highly available architecture and automation-led intelligent operations, empowers enterprises with business resiliency on a larger scale and minimum investment.
Here are a few strengths of Sify Cloud Anywhere:
- Unified dashboards
- Unified monitoring
- Multi-skilled support
- Integrated delivery framework
- Cloud connect with low latency
- Expertise in DC, Network, and Managed services
- Services for infrastructure assessment and consultation
Sify FinOps to fulfil cloud promise
Through its comprehensive FinOps capabilities, Sify offers industry-leading AI/ML-driven cloud management platforms and solutions that give organizations unified visibility into their cloud infrastructure. With Sify’s expertise and AI/ML-driven solutions, organizations can confidently navigate their cloud transformation, optimize costs, and streamline their operations for maximum effectiveness and success. Here’s how Sify AI/ML enabled cloud platform delivers-
- Cost Governance:
- Rightsizing of cloud resources by simplifying analytics on overall utilization, trending, and resource & capacity planning
- Enables multi-cloud coverage for enhanced cost optimization
- Financial domains for project management, budget control and chargeback enablement
- Real-time ML based observability:
- Real-time cloud waste analysis, smart startup & shutdown scheduler recommendations
- Anomaly detection to identify problems now than later
- Real-time observability of cost and performance metrics
Conclusion : Changing the game with AI/ML infused hybrid clouds
Automation holds significant potential at every stage of an organization’s cloud journey. Whether they are taking the first step towards cloud adoption, seeking to reduce bill shocks and manage multiple cloud ecosystems efficiently, or aiming to modernize legacy applications, AI/ML has a lot to offer. Reimaging your digital transformation with automation across multi cloud and hybrid IT requires a holistic approach. It involves tech adoption, process reengineering, and a cultural shift with the organization. By embracing automation, enterprises can unlock new levels of efficiency, scalability, and innovation while mitigating risks associated with modern IT landscape.
Sify provides a range of customizable solutions to cater to businesses of all sizes, whether they are embarking on comprehensive IT transformation initiatives, focused application migrations, infrastructure modernization projects, or adopting the lifts-and-shifts land-and-expand approach. With its diverse portfolio, Sify ensures that organizations can find tailored solutions that align with their specific needs and objectives, regardless of their scale or scope of transformation.
To learn more about Sify Hybrid and Multi- Cloud Services, visit here!
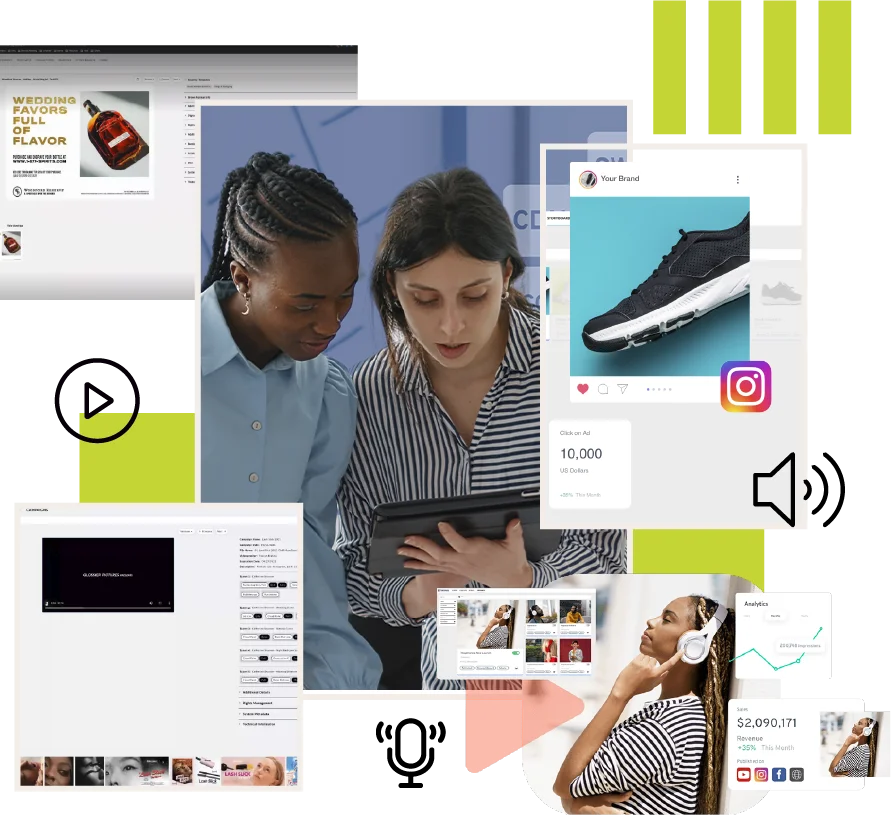
DAM Features for Effective Video Asset Management
Credits: Published by our strategic partner Tenovos.
Searching for the right digital asset management system (DAM) for video can feel like stumbling around in the dark. The time spent gathering requirements, researching applications, and reaching out to platforms can leave you more confused than before you began.
What should you actually be looking for in a DAM for video? Is a DAM even the right tool for managing your media? How can you ensure your video assets are stored and managed in a way that will optimize their usability across multiple channels and partners?
We’ll be the first to admit, there is no DAM that’s going to replace your media asset management (MAM) system for video production (though when it comes to the final asset, we’ve got you covered). But if you’re looking for instant video playback, automated metadata, and shareable portals and collections for your external partners, you’re in the right place.
In this article, we’ll set expectations for what features you should be looking for in a DAM for video assets. Make note of which features touch on your organization’s needs—it should become increasingly clear whether a DAM is right for you. Once we cover the basics, we’ll highlight why there’s so much opportunity in the future of DAM video functionality.
DAMs are made to manage your pre-distribution video assets
DAMs are ideal for managing completed video assets. The sweet spot for uploading videos to DAMs is after post-production and before marketing distribution. In this space, DAMs are essential for tracking asset usage, adding helpful metadata, and sharing assets across global teams. The best DAMs offer a suite of features that support the video’s lifecycle after publishing. But overall, you should expect most of the same functionality in DAMs for video as managing print or web assets.
Six DAM for video features you need
There is an overwhelming number of options for DAMs, each offering its own suite of features. But what do you actually need to ensure you’re getting the best DAM for video? Below is a list of the essential features every DAM should have if you’re managing video assets.
- Interoperability with existing video software
Since one platform can’t solve all your video needs, you should be looking for a DAM that seamlessly connects to your current video production or management software. Creating video is notoriously complex, but managing video in DAM shouldn’t be.Look for a DAM that integrates your existing applications and repositories to maintain the integrity of content and data when transferring video between systems. Just because assets move, doesn’t mean you should experience any data loss or lack of transparency. Good DAMs for video will connect using updated APIs with creative suites, product information management systems (PIMs), content delivery networks (CDNs), and content management systems (CMSs). - Instant global video management
World-class enterprise DAMs have no excuse for slow video playback speeds or a lack of video thumbnails. Many DAM platforms have implemented built-in CDNs to ensure you can play, share, download, and publish videos with little lag.Your DAM should be built on cloud-based architecture that allows for uninterrupted global access to the platform for all users. This ensures your DAM is regularly updated with new video functionality without impacting your workflows or security. - Review and workflow management
The best DAMs for video should be able to streamline the creative review and proofing process. Look for a DAM that can ingest your video assets and pull them into automated review workflows.Using your DAM for reviews, annotations, and approvals will enhance productivity and keep your projects on track. This saves you time and money on third-party software and endless email threads. Internal and external teams get real-time visibility and notifications, ensuring everyone is in sync and aware as your video assets are approved. - AI or automated tagging and metadata creation
AI and machine learning are phenomenally helpful when it comes to managing video assets. DAMs using AI offer features like auto-tagging and automatic speech-to-text transcripts in multiple languages. Instead of searching for a specific video in endless folders, it only takes a few clicks to discover and share subtitled videos.In fact, machine learning can automatically scan video assets and assign tags related to the products, people, and objects within your videos. Supplement that metadata by integrating your product information management (PIM) system to improve insights and discovery. All this data makes searching and managing video assets a breeze. - Role-based interfaces, collections, and portals
When choosing a DAM for video assets, personalizing each user’s experience—whether through role-based interfaces, branded portals, or sharable collections—helps you access and share your videos without interruption. Ensure any DAM you choose allows you to create secure, branded portals without worrying about size limits or other technical restrictions.Similarly, many DAMs have ‘collections’ or role-based features which ensure only the right teams, partners, and agencies view and edit certain content. With a combination of role-based dashboards, portals, and collections, you can ensure all rights management and intellectual property rules are dynamically adhered to and everyone has the videos they need. - Customizable and scalable rights and security
Last but certainly not least, your videos need to be secure and easily shareable with those who need them. As opposed to MAMs, which may only host up to 20 users, DAMs can host thousands of users signing in from anywhere in the world. If you’re looking for a DAM with scalable features, prioritize platforms with clear and customizable controls—you should be able to edit rights and access based on campaigns, teams, brands, geographies, and more. It’s also wise to explore if your DAM can automate security and rights notifications, so you can get alerted if licenses are about to expire or need renewal.Additionally, check if your DAM tracks how your content is being shared and by who. Good DAMs will have alert features that trigger users to when there are spikes in usage or unusual behavior.
What is the future of DAM for video assets?
In the future, DAM features will evolve to do even more. We’re already seeing features like AI-assisted subtitles and dynamic resizing for social channels. More innovators in the DAM space are tracking video watch data in DAM—feeding that data back into the asset lifecycle to create a closed loop of continual content improvement.
In the end, if these six features address your organization’s needs, a DAM might be right for you. Features like interoperability, workflow management, rights management, and instant global playback will set you up for DAM for video success. Don’t forget to add them to your wishlist!
After all, a journey of a thousand miles begins with a single step. Your adventure awaits.
Want to know what types of data your DAM should be providing? Reach us at marketing@sifycorp.com
Written by Michael Waldron, CMO, Tenovos
The Definitive Guide to DAM Adoption
Credits: Published by our strategic partner Tenovos.
If you’re launching a digital asset management system (DAM), you know that technology isn’t your only challenge—sometimes people are. You can have the best DAM in the industry and processes to match, but if your users don’t adhere to naming conventions or don’t categorize assets correctly, the project can devolve into a DAM quagmire. So, how do you get all the users of your DAM—from designers and partners to agencies and entire teams—to come along on your DAM adventure from the start? Your journey will involve mapping out your terrain, building your guild of allies, consulting your DAM wizards, and choosing the path to your DAM legacy.
This article will be your definitive guide to DAM adoption from the beginning. We’ll explain the process of getting users involved in selecting and rolling out your DAM, as well as the strategies you can use to ensure widespread adoption and ongoing equilibrium.
If you already have a DAM, the steps below are perfect for rethinking your adoption strategy. It’s easy for users to fall off the adoption wagon, so your strategies should be evolving to keep up. You’ll determine where to improve your engagement with your users, strengthen your desired norms, and encourage better user behaviors. From mapping out your DAM journey to setting yourself up for a legacy of success—let’s talk about how to achieve optimal DAM adoption.
1. Map out the terrain—user influence and resistance
The (not so secret) secret to DAM adoption is identifying and engaging your stakeholders early in the process. For those without a DAM (or replacing your existing DAM), it means prioritizing the needs of those who will use the DAM inside and outside your organization.
Start with a stakeholder mapping exercise—sit down and brainstorm everyone who will be using your DAM or involved in the success of implementing it. Write each name on a sticky note—from the illustrators uploading new assets, to the IT manager who will deal with support tickets. Then sort those stakeholders into quadrants:
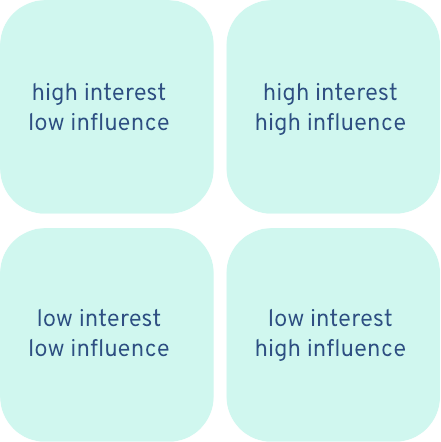
This exercise will help you determine which stakeholders should focus your energy and support on throughout the DAM adoption process.
It’s also important to conduct resistance planning. To manage resistance, you should brainstorm all the potential reasons your stakeholders might resist your new DAM—make a thoughtful, comprehensive list. Executives may lack awareness of why a change is needed. Creative teams may fear the unknown that comes along with this change. IT may resist because they anticipate a lack of support once the DAM is implemented. In this stage, you should consider your users’ concerns carefully, making note of potential blockages will help you gather their feedback and develop a communications plan that effectively addresses their concerns.
For organizations that have already implemented their DAM, it’s never too late to map your stakeholders and consider their needs. Resistance can happen at any point in the journey. Investigate how your DAM is performing with a survey, DAM usage data, or user interviews at regular intervals. You may not be able to implement a new system, but it’s never too late to revisit your users’ needs and consider why they may be resisting your processes.
2. Build your guild—recruit your DAMbassadors
After you’ve determined which users have the most influence and interest in your DAM, you should identify who among them could be your allies. Who is likely to adopt new norms quickly? Who can assist you and offer insight into team morale? Who is most invested in the DAM planning process and its success?
Determine who among your internal (and even external partners) would be willing to offer ongoing feedback and engage with the DAM process. These are your DAMbassadors and they will help you disseminate information, encourage excitement in your engagement campaigns, and uphold the norms and processes you’ll put in place.
Recruiting them could be as easy as taking the ‘high interest/high influence’ users from your stakeholder mapping and asking if they’d be interested in taking on an advisory role. It could be for a limited time as the DAM is selected and implemented, or if your DAM is already in place, you could ask them to give feedback on an ad hoc basis. Consider incentivizing this role—people are more likely to feel appreciated if they gain something from their insights. Bonus points if some of your champions are executive-level leaders—their buy-in will be important to secure budget and support across the organization.
Learn pro-tips on Maximizing your Content Value
3. Consult your wizards—plan your processes and collect feedback
It’s never too early to start thinking about governance, or how your DAM will be managed. As a part of governance, you must define processes related to users, assets, metadata, and uploads.
You will need to answer questions like:
- Will assets be uploaded manually through the DAM, via an integration, or both?
- Are you managing web assets? Video assets? Something else? How does that change your DAM needs?
- What are your file naming conventions? And where are these documented, and how are they communicated and enforced?
- Which users/groups will be permitted to edit metadata?
- Who will be responsible for archiving and expiring files?
- Who will provide DAM access to external users? Who will be responsible for training them?
- What are the different levels of access/permissions for different users and groups? How will access change if the users are external agencies, vendors, or retail partners?
Building and documenting these norms early on allows you to run them by your DAMbassadors and important stakeholders to ensure you’re considering complex user or asset challenges that may come up when choosing, implementing, or managing your DAM.
And remember that feedback shouldn’t stop at the planning stage or after you’ve implemented your DAM—continue seeking ongoing feedback from your internal stakeholders and external DAM users. Nothing halts adoption more than users feeling like their feedback and suggestions don’t matter. Consider how you can collect feedback throughout the DAM process and follow up if user feedback influenced a decision—this builds their trust.
4. Pick your path—select the best DAM for your needs
Once you’ve determined your DAMbassadors, your unique governance idiosyncrasies, and sought the feedback of your internal and external users, you’ll be ready to select your DAM.
Picking the right DAM can often feel endlessly complicated—the time spent gathering requirements, researching applications, and reaching out to platforms can leave you feeling exhausted by the options. Narrow your focus on the top features that your organization cannot function without—based on your stakeholder feedback, of course. If you’ve done Steps 1-3 thoroughly, your organization’s ideal DAM should check off all your most important boxes.
If you’ve made your case to your executive-level leadership, done your research, and considered user feedback, your choice of DAM should set you up for the ideal user adoption scenario.
5. The rallying cry—develop and execute a communications plan
Communication plans can make or break DAM implementation. A clear comms plan will ensure everyone knows how the DAM will help them achieve their goals (i.e. what they can expect from the DAM) and how they’re involved in the implementation and management of the DAM (i.e. what’s expected of users). Use face-to-face meetings, town halls, forums, and Q&A sessions to communicate with stakeholders.
The key message is simple: If the DAM works as intended and users adopt it as directed, everyone’s lives become easier. This plan defines the philosophy of the DAM, how it will be used, and how success will be measured for all users. It should include a timeline for implementation and onboarding and where users can go for ongoing DAM best practices, support, and training. You may choose to include how your organization plans to work with the DAM vendor and how the transition from the current asset system to the DAM will take place. The more clear and thoughtful your comms plan is, the more likely you’ll be to reduce friction post-launch and improve adoption.
6. Create a legacy—make onboarding and ongoing training impossible to ignore
Your DAM adventure has begun. It’s filled to the brim with users accessing your DAM for many reasons—approval workflows, sharing assets, archiving past campaigns. How do you manage to keep all those users following your carefully curated governance rules and norms? You create onboarding and training tools that are tailored-made to teach. Here are 3 DAM onboarding and training ideas to keep your journey of asset management smooth:
- Launch a frequently asked questions (FAQ) video series in your DAM
Take a page out of Webflow University’s book and make a library of quick videos to onboard users, answer common questions, and reiterate helpful governance norms. Host your FAQ library in your DAM and link its location to the dashboard of every user. Each video can be casual and even funny—the point is to make learning and relearning DAM conventions accessible and impossible to ignore. - Create a DAM help desk
Sometimes users don’t know where to get their questions answered. Creating a DAM help desk, either in person or virtually, gives them a predetermined window to come to you with questions and feedback on the DAM. Have your DAM managers, IT staff, or DAMbassadors cycle through ‘office hours’—they can be on standby until a user reaches out with a question. This also works great asynchronously as a Slack or Teams channel. - Build a governance document
Remember the governance planning you did in Step 3? Consider creating a governance resource that users can refer back to. Create an artfully designed landing page—an internal search engine that points people to common solutions to their problems. Give clear guidance on how to use common metadata terms, manage metadata, and upload assets. Include anything else that users may forget or make mistakes from time to time.
You may notice that this resource and your video FAQ library will have some overlap—it’s important to have resources available in multiple formats and places. The more accessible, interesting, and valuable this information is, the more likely your users are to adopt it.
Your DAM adoption journey begins with a single step
User adoption is the single defining characteristic of a successful DAM implementation. Are your users accessing the DAM as intended? Is it working for them as intended? In your DAM adventure, user adoption is an ongoing process—a never-ending story. But, if you can map out your desired digital asset system, bring along the right users to see it through, plan and communicate your processes, and keep people engaged—widespread adoption is possible.
For organizations with entrenched DAMs (and tired DAM managers), it’s never too late to address user adoption. There’s always the opportunity to seek feedback on how to improve your DAM processes, make training easier to access, or develop a comms plan that revitalizes users’ desire to make the DAM better.
After all, a journey of a thousand miles begins with a single step. Your adventure awaits.
Want to know what types of data your DAM should be providing? Reach us at marketing@sifycorp.com
Written by Michael Waldron, CMO, Tenovos
Rise with SAP… (But how?)
– An article by Prashant Pimpalekar, covered by Enterprise World
SAP has ramped up a bulk of its resources, innovations and R&D investments to transition SAP Business Suite/ERP customers (i.e. on SAP ECC6.0) to SAP S/4 HANA on Cloud. The campaign it launched worldwide (“Rise with SAP”) has been well-received by its customers and prospects.
While SAP has provided multiple choices for the said transition, it has created some confusion in customers’ minds. Rise with SAP but how? Which way to go? What is the best option suited for my organization?
Instead of directly telling the options available under Rise with SAP (deployment models for S/4 HANA Cloud), this article takes a customer-centric view and provides multiple scenarios of SAP customers/prospects and recommendations for the best-fit possible.
- Yours is a startup raring to go. You want an ERP software which will provide a rich functionality of all the key business processes (right from procure to pay, order to cash, record to report, hire to retire etc.) seamlessly integrated, can accommodate the scorching business growth, would be Cloud-based (and so scalable) with subscription-based pricing giving SLA-bound performance with lowest possible TCO (Total Cost of Ownership). And all this in record time, ready to run! In this case, SAP S/4 HANA Cloud (Public Edition) could be the best option.
- Or, you head a lean organization with SAP ERP ECC6.0 implemented (or you could be on a lower version of S/4 HANA, say 1503, on-premise), say, 6 to 8 years ago. In that long period, your SAP system has been customized on many instances to meet the business requirements on an ad-hoc basis. Due to various reasons, master data quality has not been up to the mark. Customizations done years ago seem to be no more relevant in the changed business scenario of today. Overall, the SAP deployment satisfaction index is not high. Given a chance, you would like to discard the chaotic system and start afresh on a blank slate. But while doing it, you don’t want to lose the rich functionality of integrated and reliable business processes and the comfort of SAP users. Keeping in tune with the changing times, you want to avail the elasticity of Cloud, want to see greenfield Implementation of SAP S/4 HANA in record time with a competitive budget. In this case, SAP S/4 HANA (Public Edition) could be the best option.
- Or, yours is a big organization with SAP ERP ECC6.0 implemented, say, more than a decade ago. Most of the key business processes have been mapped and are being used across many plants, branches spread across the country (or even across many nations). Mirroring the business, the business processes are complex and due customization has been done to cater to local/country-specific requirements. You have maintained relatively high data hygiene in the SAP system and the SAP deployment satisfaction index is pretty good. You can’t afford to lose all that and so can’t think of any greenfield implementation. Your organization also puts much more emphasis on security and so want to go for single-tenant tenancy on Cloud. In that case, Brownfield migration to SAP S/4 HANA Cloud (Private edition with Hyperscaler) could be the best solution. The SAP system/servers could be hosted on one of the hyper-scalers like AWS, MS-Azure or GCP (Google Cloud Platform).
*Brownfield migration- Here you are getting SAP master data, transactions, configured business processes, RICEF objects, balances from SAP ECC6.0 into S/4 HANA (whichever is the target version). No need to create them from scratch (or upload them via batch programs). It also gives you an opportunity to configure new business processes, rectify some old processes, add any enhancements etc. if you perceive a need.
- Or you are a CXO of a very large organization using SAP ERP ECC6.0 say, since more than a decade. Most of the key business processes have been mapped and are being used across many plants, branches spread across the country (or even across many nations). Mirroring the business, the business processes are fairly complex and due customization has been done to cater to local/country-specific requirements. You have maintained relatively high data hygiene in the SAP system and the SAP deployment satisfaction index is pretty good. You can’t afford to lose all that and so can’t think of any greenfield implementation. Besides, your organization works in a highly regulated environment (federal/state/local regulations) like life Sciences / Utility / BFSI putting heavy emphasis on various compliances. So besides opting for single-tenant tenancy on Cloud, you also want the SAP system/servers residing on a designated private data center (like HP, Dell, Lenovo). In that case, Brownfield migration to SAP S/4 HANA Cloud (Private edition – Customer data center) could be the best solution.
Following table captures the essence of above explanation along with some important data points (which could not be covered earlier) which should assist in your decision-making process of S/4 HANA migration.
RISE with SAP Deployment Models for S/4 HANA Cloud –
| Public Edition | Private Edition Hyperscaler | Private Edition Customer Data Center | |
|---|---|---|---|
| Business driver | Ready to run | Tailored to fit | Data sovereignty/residency, performance, security, portability |
| Service offering | SaaS (SAP) | IaaS & PaaS (SAP) | IaaS (HP/Dell/Lenovo) & PaaS (SAP) |
| Migration type | Greenfield only | Greenfield or Brownfield | Greenfield or Brownfield |
| Licensing model | Subscription- Cloud ERP | Subscription- Cloud ERP | Subscription- Cloud ERP |
| SAP SLA % | 99.7% | 99.7% | 99.7% |
| Tenancy | Multi-tenant | Single-tenant | Single-tenant |
| Max scale up RAM | 6 TB | 24 TB | 24 TB (with HP), 12 TB (with Lenovo), 6 TB (with Dell) |
| IaaS data center location | SAP’s choice | Choice of public cloud data centers | IaaS (with customer data center choice) |
| Infrastructure host | AWS, Azure, GCP, SAP | AWS, Azure, GCP | HP, Dell, Lenovo |
| Cloud deployment | Public cloud | Public cloud | Private cloud |
| Data management and storage | Shared | Shared | Dedicated |
| Customization | No | Yes | Yes |
| SAP source code changes | No source code changes No IMG access | Yes | Yes |
| Upgrade flexibility | No (Compulsory 2 upgrades/releases every year) | Yes (customers can choose when to upgrade) | Yes (customers can choose when to upgrade) |
| Integration with SAP PO (Process Orchestration) | Not possible | Yes | Yes |
Conclusion –
Scenarios explained above need to be taken with a pinch of salt. It is highly possible that even a large organization may discard their current SAP system and may go for greenfield implementation, or a unicorn startup may go for Private edition (Hyperscaler). It all depends on N parameters (some of which are discussed above), budget, timeline expectations etc. So, while there is no one-size-fits-all nor is any solution right or wrong, this article should assist the CXOs in deciding which way to go for SAP S/4 HANA migration.
Check out the full feature here
Data Center Automation – Exploring Opportunities and Addressing Challenges
In the grand tapestry of India’s digital journey, data center automation is a defining thread that weaves excellence, resilience, and growth into the very fabric of the nation’s IT landscape. The amalgamation of innovation and automation empowers data center companies to transform operations, elevate security, and unlock new levels of efficiency. As the scale and complexity of data management continue to escalate, the role of automation in data centers has emerged as a transformative force. From provisioning and configuration management to monitoring and security, automation is the catalyst behind operational efficiency, reduced human intervention, and remarkable precision.
Data center automation involves the use of advanced technologies like AI/ML and robust software to streamline & orchestrate various data center processes. This automation enables data centers to operate tasks that were previously time-consuming, error-prone, and labour-intensive. These tasks can now be automated, leading to optimized resource utilization and improved overall performance. With the right approach, data center automation can revolutionize the digital IT landscape, enabling businesses to stay agile, competitive, and future-ready.
India’s Data Center Landscape: A catalyst for Innovation
India is becoming the preferred data center destination for enterprises and hyperscalers. Currently, there are 138 operational data centers in India, utilizing 737 MW power. Over the next 3-4 years, an additional 50 data centers are expected to be established, resulting in a power demand of 1050 MW. Indian cities like Chennai, Hyderabad, Bengaluru, Mumbai, Pune, Noida, and Kolkata are emerging as data center hubs, hosting a myriad of providers catering to diverse industries. Several leading companies leverage automation techniques to deliver seamless and reliable solutions to their clients. The adoption of automation has enabled them to offer cost-effective services, rapid deployment, and robust security measures.
Important Role of Virtualization
Virtualization forms the crux of data center automation, particularly in cloud computing environments. By abstracting hardware resources and creating virtual machines (VMs), data center administrators can deploy and manage applications more efficiently. Virtualization allows for dynamic allocation of resources, on-demand scalability, and workload migration across servers. This flexibility streamlines automation processes and optimizes resource usage. It enables data centers to adapt and scale rapidly according to their requirements.
Benefits of Data Center Automation
Data center automation presents a world of opportunities for businesses in India and around the globe. The opportunities presented by automation are vast, ranging from operational efficiency to enhanced resource utilization. Data centers must automate to experience the following benefits:
- Enhanced Efficiency: Automation propels data centers into an era of unparalleled efficiency by eliminating manual intervention. Time-consuming routine tasks, once automated, can be executed with precision, freeing up skilled personnel to focus on strategic endeavours. By automating resource allocation and workload management, data centers can achieve optimal utilization of computing power, storage, network resources, and automate incident response. This efficiency translates into reduced downtime, optimized power consumption, better hardware utilization, improved operational efficiency, cost savings, better scalability, and a greener footprint.
- Faster Deployment & Flexibility: Automation expedites the deployment of applications and services in a data center. With automation’s ability to swiftly allocate resources on demand, data centers become more agile and responsive to changing workloads. This scalability ensures optimal performance, even during traffic spikes or resource-intensive tasks. Automated Data Centers embody flexibility by seamlessly adapting to evolving business needs. Through intelligent automation, these facilities can swiftly deploy new services or applications as demand fluctuates. This adaptability ensures that businesses can respond to changing market conditions and customer demands with agility, without the constraints of static infrastructure.
- Enhanced Security Posture: Automated security protocols keep a constant vigil on data center environments. Threat detection and accelerated incident response help prevent cyber threats and potential breaches. Automated security measures aid in responding promptly to security incidents. This proactive approach enhances data center security, protecting sensitive data and critical systems.
- Rich Data Insights and Analytics: Leveraging the power of automation and advanced monitoring systems, the data centers constantly collect more and more data on business performance, resource utilization and system health. The data analytics provides businesses with valuable insights into their IT infrastructure. This insight empowers organizations to make data-driven decisions, optimize resource allocation, predict maintenance needs, and improve overall efficiency.
- Cost Savings: Automation led data centers help save costs through energy efficiency, resource management, predictive analytics & maintenance, scalability, labor efficiency, error reduction, location optimization, integration, and compliance management These cost-saving benefits make automation a strong investment for businesses looking to optimize their IT systems.
Challenges in Data Center Automation
While the benefits of data center automation are compelling, embracing automation comes with its own set of challenges. Many data centers consist of heterogeneous systems and technologies, making it difficult to integrate new automation tools seamlessly. Here are a few challenges that data centers may face while embracing automation:
- Skills Gap: Introducing automation into existing data center infrastructures demands careful planning and integration. Besides, adopting automation requires skilled personnel who can manage and maintain the automated processes. Data center staff may need to upskill or reskill to effectively leverage these automation tools. They must evolve from playing traditional roles to becoming adept orchestrators of automated workflows and processes.
- Security Concerns: As automation reduces manual intervention, robust security measures become paramount. Safeguarding against unauthorized access and potential vulnerabilities is imperative. Data centers must keep an eye for unauthorized access to automation systems or potential misconfigurations, which could lead to severe data breaches and service disruptions..
- Large Initial Investment: The initial capital investment required to implement automation tools and technologies can be significantly high. Smaller data center companies in India may find it challenging to invest in these technologies, limiting their ability to compete effectively. While the long-term benefits are substantial, data center companies must carefully assess the need for capital investment against the potential gains they offer.
- Regulatory Non-compliance: Automation may raise concerns about non-compliance with industry standards and data protection regulations. Hence, data center companies must ensure their automated processes comply with the industry standards and regulations including Personal Data Protection Bill (PDPB), ISO 27001, Payment Card Industry Data Security Standard (PCI DSS), Telecom Regulatory Authority of India (TRAI), ISO 14001, and more.
Transforming Data Centers With Sify Technologies
Sify Technologies has been a pioneer in the India data center services market, serving enterprises for more than two decades. We have been delivering value to our customers by enabling them to achieve their digital transformation goals, powered by intelligent data center automation. Sify data centers provide automation benefits such as better visibility into the data center operations, while ensuring optimum utilization of resource capacity. Paving the way for innovation and growth, we are not only transforming data center operations but also contributing to building India’s tech landscape.
The integration of AI/ML-based predictions plays a crucial role in managing availability, performance, cost, and capacity. Currently, Sify data centers commits:
- 8-10% savings on PUE
- Improving equipment time by 20%
- Up to 300 person hour savings in a month
- 20% reduced MTBF, 10% improved MTTR, and 10% reduction in unplanned/possible downtime
- reduction in customer penalties by maintaining SLAs
- 10% reduction in operating cost
Conclusion
In conclusion, the field of data center automation offers countless opportunities for organizations to increase efficiency, scalability, and reliability in their business. Adoption of automation technology can enable routine tasks simplify, reduce human error, and free up IT staff for more strategic efforts. However, it is important to acknowledge and address challenges such as security concerns, skills gaps and the need for better planning and management. With a strategic thinking approach, organizations can unlock the full potential of data center automation, paving the way for faster and more agile digital processes in a data-driven world.
Accelerate your digital transformation journey with a digital-ready IT infrastructure powered by Sify. Learn more about how Sify can transform your organization by becoming your digital infrastructure partner.
Choosing the right Managed Wi-Fi provider- Key Considerations
In today’s hyper-connected world, a stable and efficient Wi-Fi network is essential for enterprises to operate seamlessly. A robust and dependable Wi-Fi network is the foundation of success for any thriving business, facilitating seamless employee communication and offering a platform for engaging with customers.
Managed Wi-Fi providers offer a range of services, designed to make your Wi-Fi network hassle-free and optimized for performance. But how to choose the right managed Wi-Fi provider? In this article, we will explore the key factors you must evaluate when making this decision.
Understanding your core requirements
Before beginning your search for a managed Wi-Fi provider, it is crucial to understand your core requirements. It might depend on your business type, size, number of devices connecting to network, bandwidth & coverage needs, security demands, compliance, and more. Here is a list of essential features and services your potential managed Wi-Fi provider must offer.
- Performance
The foundation of successful business operations is a stable and high-performance Wi-Fi network. When evaluating managed Wi-Fi providers, prioritize reliability and speed. Downtime or slow connectivity can disrupt operations and negatively impact potential lead interactions. Ensure the provider can offer Service Level Agreements (SLAs) with guaranteed uptime and performance levels that meet your business needs.
- Scalability
One of the most critical considerations when choosing a managed Wi-Fi provider is scalability. Your network needs may change over time as your business grows or usage patterns evolve. Look out for a partner that can accommodate scaling up or down without significant disruptions. Ask potential providers about their scalability options and whether they can adapt to your future requirements.
- Reliability and Redundancy
A reliable Wi-Fi network is a non-negotiable requirement for businesses. Downtime can lead to lost revenue, frustrated customers, and decreased productivity. When evaluating managed Wi-Fi providers, inquire about their network reliability and redundancy measures. Look for providers with a track record of minimal downtime and robust failover solutions to ensure uninterrupted service.
- Security
Cybersecurity threats are constantly evolving, and your network must be protected from potential breaches and attacks. Make sure your provider offers robust security measures such as firewall protection, intrusion detection, and encryption. Additionally, inquire about their approach to security updates and patches to stay ahead of emerging threats.
- Quality of Service (QoS)
Different devices on your network may require varying levels of bandwidth and priority. For example, video conferencing and voice-over-IP (VoIP) calls demand low latency and consistent bandwidth. A managed Wi-Fi provider that offers Quality of Service (QoS) allows you to prioritize traffic according to your needs, ensuring a seamless user experience for critical applications.
- Network Management and Monitoring
Effective management and monitoring are essential for maintaining a healthy Wi-Fi network. Your managed Wi-Fi provider should offer robust tools and platforms that allows you to monitor network performance, troubleshoot issues, and make necessary adjustments. Look for providers that provide real-time visibility into your network’s status and offer proactive support to address potential problems before they impact users.
- Support and Service Level Agreements (SLAs)
Consider the level of support your managed Wi-Fi provider offers. What are their service level agreements (SLAs)? Do they provide 24/7 customer support? Can they respond quickly to network issues? Clear communication and reliable support are crucial, especially during network emergencies. Ensure that provider support offerings align with your business needs and expectations.
- Cost and Pricing Structure
Cost is undoubtedly a significant factor when choosing a managed Wi-Fi provider. Some providers might charge based on the number of devices connected, while others may have data usage-based pricing. Make sure you are aware of any potential hidden fees or overage charges and choose a pricing model that aligns with your usage patterns.
- Compatibility and Integration
Consider your existing technology infrastructure when selecting a managed Wi-Fi provider. Will the provider’s solution seamlessly integrate with your current systems, such as point-of-sale (POS) systems, security cameras, or other IoT devices? Compatibility and integration capabilities can significantly impact the efficiency and effectiveness of your network.
- Reputation and Reviews
Finally, research the reputation and customer reviews of potential managed Wi-Fi providers. Online reviews and testimonials from current clients can provide valuable insights into a provider’s performance, customer service, and overall satisfaction. Additionally, inquire about case studies or references to gain a deeper understanding of how the provider has helped businesses similar to yours.
Sify Edge Connect: One-stop Solution for your Managed Wi-Fi needs
Sify Edge Connect is a comprehensive suite of services involving Edge connect Advisory and Implementation services combined with wireless management and intelligent edge analytics. It is a fully managed secure wireless platform that integrates IT, OT, and people. Edge Connect offers a seamless expansion of its core services to edge devices while delivering centralized management for streamlined operations, infrastructure near the end-user for reduced latency, and expert management of policies for data protection.
A few salient features of Sify’s Edge Connect are:
- Cloud-based centralized management platform
- Controlled Internet access to guest users with GIS mapping
- Highly scalable and resilient
- Pan India deployment & support
- Service-based model with end-to-end ownership
Wrapping Up!
Choosing the right managed Wi-Fi provider is crucial decision that can impact your business efficiency, security, and customer satisfaction. By carefully understanding above factors, you can make an informed choice that aligns with your specific needs and goals. A well-chosen managed Wi-Fi provider will ensure a reliable wireless network and empowers you to focus on what matters most while growing your business and serving your customers.
Boost your network edge for all-round digital transformation with Sify’s Edge Connect now!